The Certificate Hierarchy Root, Intermediate, and Leaf Certificates
Have you ever wondered what that little padlock icon in your browser really means? Or websites keep your data safe from prying eyes? Behind that padlock lies a system of digital certificates. These certificates verify identities and encrypt communication online. Certificates aren’t just for public websites they also play a crucical role in securing servers, internal services and closed systems you might run in your homelab or enterprise network. Whether its encrypting traffic between applications or ensuring that only authorized parties can communicate certificates are fundamental to building trust on the internet and behind the scenes.
Root
The first link in the certificate chain Root Certificate called the trust anchor. This certificate is self-signed and highly proteceted often kept offline in secure environments.
Root certificates are important because they form the foundation of trust for all certificaftes beneath them. Itermediate and finally leaf certificates. When a root certificate private key is used to sign an intermediate certificate that intermediate inherits trust from the root. As intermediates issue certificates further down the chain, trust cascades enabling clients (such as web browsers or operating systems) to verify identities and encrypt communications securely.
Root certificates are handled with extreme care. They are usually stored offline within highly secure hardware modules and protected by strict policies and procedures. They are distributed pre-installed in trusted root stores embedded in operating systems, browsers, and applications—so that your device already “knows” which root certificates to trust.
Why do we trust the root? Because they come securely installed by a trusted party (like Microsoft, Apple, or Mozilla). Managing root keys is so sensitive that Certificate Authorities (CAs) perform signing operations only during highly secure signing ceremonies, usually performed offline by multiple trusted operators ensuring keys are never exposed to reckless environments.
Intermediate
An Intermediate Certificate aka the subordinate CA certificate is the middle layer in the certificate chain between the root and leaf certificates. Different from the root certificate which is self-signed a intermediate certificate is signed by either the root certificate or another intermediate certificate. This allows Certificate Authorities to offload the responsibility of issuing certificates to intermediates while keep ing the the root safe.
Since root certificates are very sensitive and kept offline in secure environments they are rarely used directly to issue end certificates (the leaf certificates you encounter on websites and devices). Instead the intermediates handle the day to day task of certificate issuance acting as the gatekeepers. This structure protects the root from exposure and potential compromise.
If an intermediate certificate is compromised it can be revoked or replaced without invalidating the entire PKI infrastructure limiting damage and preserving trust in the system. Intermediate certificates usually have a shorter lifespan 10 to 15 years to maintain security through regular renewal.
Leaf
Leaf certificates are the final link in the certificate chain. Different from root or intermediate certificates leaf certificates cannot issue other certificates they are issued to actual users, devices, and or servers.
These certificates contain identifying information such as the domain name for a website the name of an organization, or device details along with the public key associated with that entity. When visiting a website over HTTPS, the server presents its leaf certificate to your browser, which then verifies its authenticity by following the certificate chain back to a trusted root.
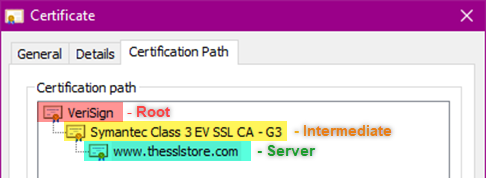
Leaf certificates are signed by the intermediate certificate authorities inheriting the chain of trust. Their primary role is to enable encryption and authenticate identity so that data exchanged between the clients and the servers remains confidential and tamper-proof.
Leaf certificates are used actively on servers and client devices their lifespans are relatively short usually ranging from a few months up to a couple of years to reduce risks related to key compromise or vulnerabilities. We are also in a time where 6-day certifcates could soon be a thing
How are they used in TLS handshakes?
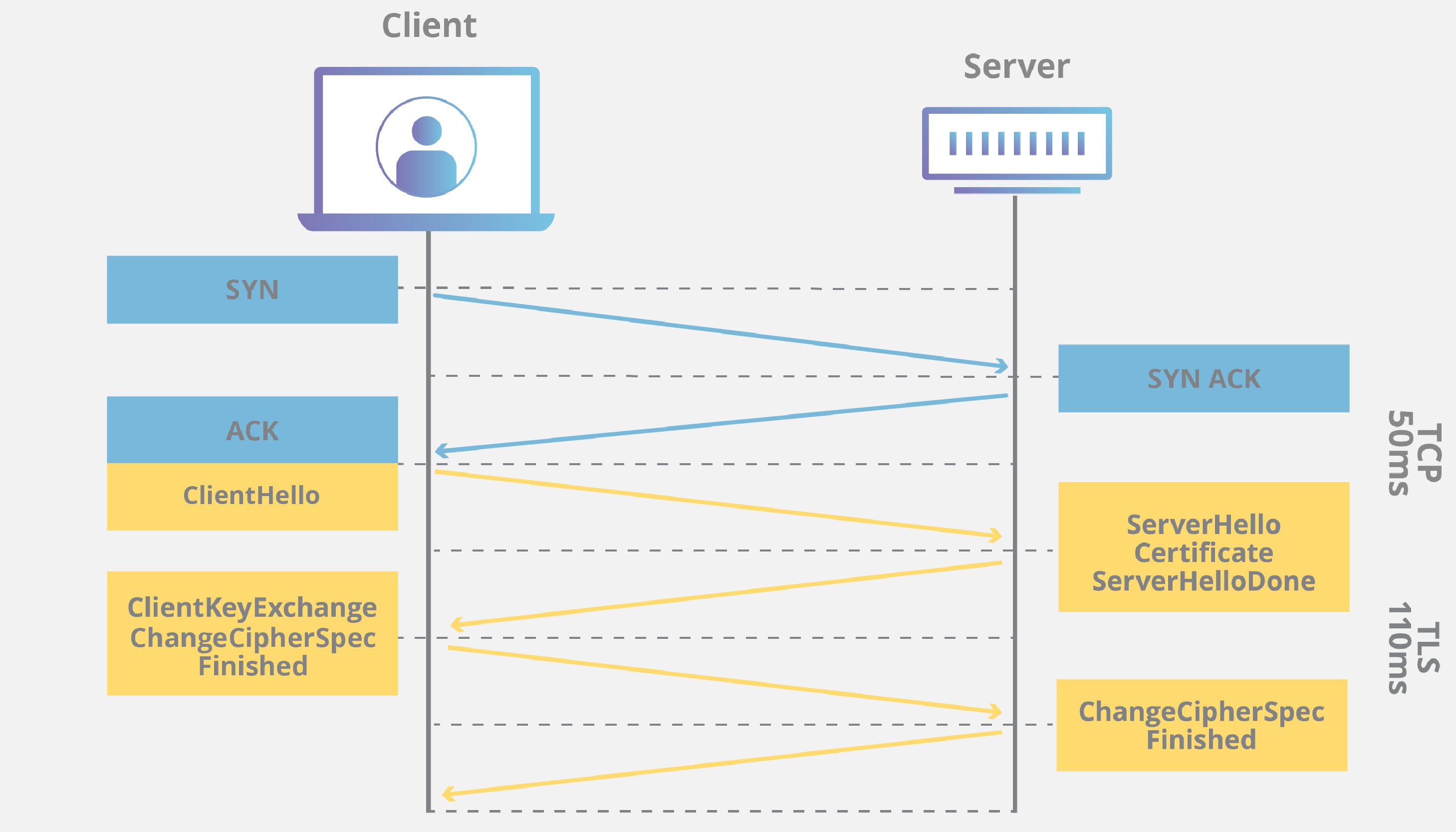
A basic rundown of the TLS handshake can be seen below. (The video below does a much better job of explaining it then I do)
-
ClientHello: When you visit an HTTPS your browser sends a ClientHello message to the server indicating its supported TLS versions and cipher suites.
-
ServerHello: The server replies with its chosen TLS version and cipher suite.
-
Server Certificate: The server sends its leaf certificate (along with any intermediate certificates) containing its public key and identity information.
-
Verification: The client verifies the server’s certificate by checking that it is valid, not expired, matches the domain name, and that its signature chains back to a trusted root stored in the client’s trust store.
-
Key Exchange: Once verified the client generates a pre master secret (a temporary key), encrypts it using the server’s public key from the certificate and sends it to the server.
-
Session Key Derivation: The server decrypts the pre-master secret using its private key. Both parties then use this secret and random data exchanged earlier to derive the same symmetric session key.
-
Secure Communication: From this point all communication uses symmetric encryption with the session key for confidentiality and integrity which is less resource intensive than asymmetric encryption.
Certificates might seem invisble most of them time (Until they expire) but they are constantly working behind the scenes to protect your communications and verify identities across the internet. From the guarded root certificates that serve as a anchor for the system or the intermediate certificates that handle day to day operations. Finally down to the leaf certificates that secure individual connections each layers plays a important role in the the chain of trust.
Understanding certificates isnt academic knowledge its the secret protecing the internet. Whether you are spinning up HTTPS for a web server or wrangling mutal TLS authentication between systems or going full nerd and building our own certificate authority in your homelab. Knowing how these pieces fit together transforms you from someone weho clicks “accept” to someone who actually gets what’s happening under the hood. The next time you see the padlock icon you will know there is an entire infrastructure of cryptographic trust standing behind it.